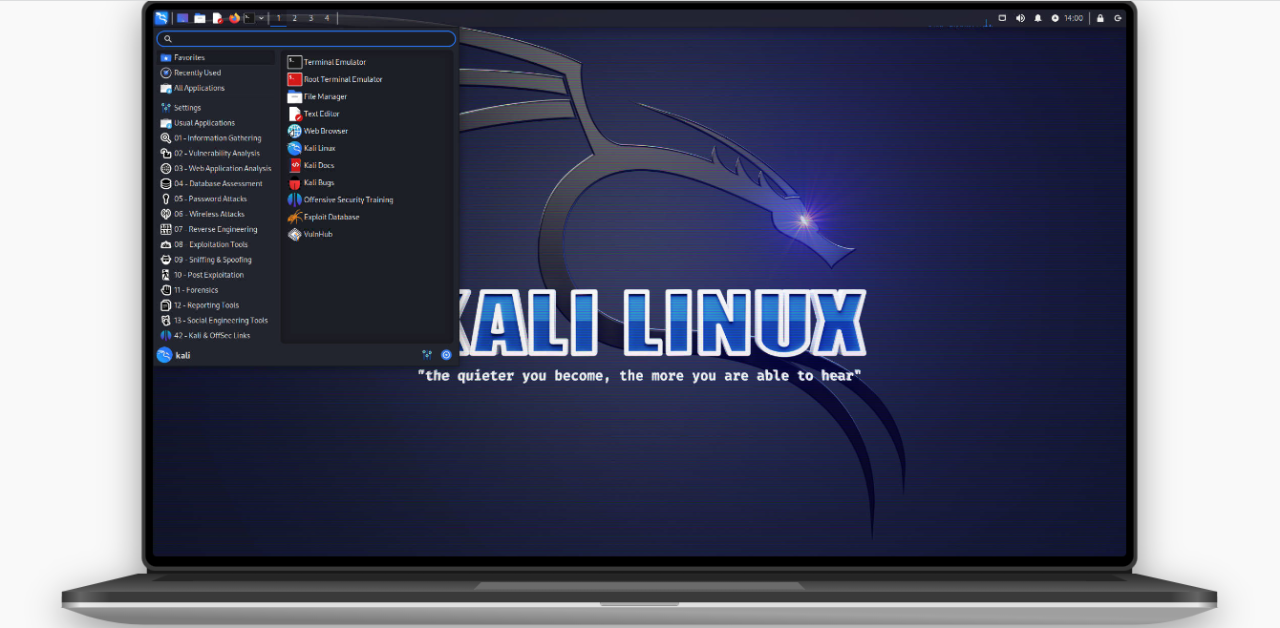
10 THINGS TO DO AFTER INSTALLING KALI LINUX 2025
Kali Linux is a powerful penetration testing and security auditing distribution used by cybersecurity professionals and ethical hackers. However, after installation, there are several essential steps you should take to optimize security, performance, and usability.
Here are the top 10 things to do after installing Kali Linux 2025, along with useful commands:
1. Update and Upgrade Kali Linux
Before doing anything else, ensure your system is up to date to patch security vulnerabilities and install the latest tools.
sudo apt update && sudo apt upgrade -y sudo apt dist-upgrade -y sudo apt autoremove -y
2. Install Missing Firmware (Wi-Fi & Drivers)
Some hardware (especially wireless cards) may need additional firmware.
sudo apt install firmware-linux firmware-realtek firmware-atheros -y
3. Configure Default Non-Root User (Security Best Practice)
Running Kali as root is risky. Instead, create a standard user:
sudo adduser yourusername sudo usermod -aG sudo yourusername # Grant sudo privileges
4. Install Essential Tools (Optional but Recommended)
Kali comes with many tools, but you might need additional utilities:
sudo apt install -y git curl wget net-tools terminator htop neofetch
5. Enable & Configure Firewall (UFW)
A firewall helps secure your system from unauthorized access.
sudo apt install ufw -y sudo ufw enable sudo ufw status verbose
6. Install & Configure a VPN (For Privacy & Security)
Using a VPN is crucial for anonymity during testing.
sudo apt install openvpn -y # Import VPN configs (e.g., ProtonVPN, NordVPN)
7. Customize the Terminal & Shell (Zsh + Oh-My-Zsh)
Improve your terminal experience with Zsh:
sudo apt install zsh -y sh -c "$(curl -fsSL https://raw.githubusercontent.com/ohmyzsh/ohmyzsh/master/tools/install.sh)"
8. Enable Automatic Updates
Keep your system secure with automatic updates:
sudo apt install unattended-upgrades -y sudo dpkg-reconfigure unattended-upgrades # Enable auto-updates
9. Install Virtualization Tools (Optional for Labs)
If you run virtual machines (VMs), install VirtualBox or QEMU:
sudo apt install virtualbox -y # OR sudo apt install qemu-kvm libvirt-daemon-system -y
10. Harden SSH Security (If Using Remote Access)
If you enable SSH, secure it properly:
sudo systemctl enable ssh --now sudo nano /etc/ssh/sshd_config # Disable root login & change port sudo systemctl restart ssh
Bonus: Install Popular Penetration Testing Tools
Some tools may not be pre-installed. For example:
sudo apt install -y gobuster seclists sqlmap john theharvester
Final Thoughts
Kali Linux 2025 is a powerful OS, but proper setup ensures security, stability, and efficiency. By following these steps, you’ll have a well-optimized system ready for penetration testing, ethical hacking, or cybersecurity research. At THE ICT WEB, we prioritize robust cybersecurity practices to safeguard digital assets and mitigate threats. As part of our security toolkit, we utilize Kali Linux 2025—a cutting-edge penetration testing and ethical hacking platform designed for advanced security assessments, vulnerability analysis, and defensive hardening.
Feel free to reach out to us for your training needs today at + (256) 781 353987 or drop us an email at [email protected]. Let’s embark on a journey towards innovation and excellence together!
Stay Secure, Stay Ethical!






